
Tess Frazier is the Chief Compliance Officer at Class. She’s built her career in education technology and believes a strong compliance, data privacy, and security program benefits everyone.

Tess Frazier is the Chief Compliance Officer at Class. She’s built her career in education technology and believes a strong compliance, data privacy, and security program benefits everyone.
We’re proud to announce that Class recently passed its Service Organization Control (SOC) 2 Type II audit. The independent audit verifies that our security controls and processes are operating effectively, and is a significant milestone in our commitment to safe and secure learning for our corporate and education customers and our partners.
The accelerated transition to digital over the past few years has provided new flexibility and convenience in how we live, work, and learn. But with these benefits comes risk: as our virtual lives become more integrated with our reality, the potential impacts become greater, especially with cyber security.
Trust and transparency are especially important in a successful learning environment. Without robust security and privacy standards and controls throughout the system, safe spaces where learners grow and thrive cannot exist.
Successful completion of the SOC 2 Type II audit provides our customers and their stakeholders with validated assurances that the safeguards we use to protect customer data are best-in-class. Our customers can feel confident that we are making every investment to establish and maintain the highest level of security and compliance.
Developed by the American Institute of Certified Public Accountants (AICPA), SOC 2 is the leading industry standard for evaluating vendor security management and defines rigorous criteria for information security and managing customer data. Key components of the SOC 2 Type II report are the verification of internal business and technology controls which have been designed and implemented to meet the requirements of the AICPA Trust Services Criteria.
The SOC 2 Type II examination process means that during the audit period, a third party monitored key business and technology processes that can impact uptime, security, privacy, and performance of a system. Upon completion, a report is published documenting the findings and details of these systems and processes so there is assured transparency for anyone doing business with an audited organization, like Class.
Put another way, in the world of cloud computing, security, availability, confidentiality, and privacy are more than what’s “in the code” – the realization of these principles also relies on how the business operates. Day-to-day operations like background checks in recruitment, financial controls, physical security, individual device security, employee training for security practices, and much more, all contribute to a secure digital environment for customers and their learners
Class worked with independent auditor, Johanson Group, to produce our SOC 2 report. It includes the following elements:
A safe and secure environment is one of the bedrock components of learning. Class, from its founding, has invested in ensuring our platform protects your organization and, importantly, your learners as they regularly use our systems to have more engaging and impactful learning. While a big milestone, our SOC 2 audit is just another step in a long road of investing in security, privacy, confidentiality, and availability that stretches back to our beginnings.
For customers and prospects, Class’s SOC 2 report is available for review by anyone who is tasked with maintaining the security of the organization’s data, privacy, and confidentiality. In many places, this might be an IT department or leadership team. This document often helps to make the process of vetting new technologies quick and seamless given many key questions are answered in the report. To access the report, please visit Class’s Trust Center.

Tess Frazier is the Chief Compliance Officer at Class. She’s built her career in education technology and believes a strong compliance, data privacy, and security program benefits everyone.

Tess Frazier is the Chief Compliance Officer at Class. She’s built her career in education technology and believes a strong compliance, data privacy, and security program benefits everyone.
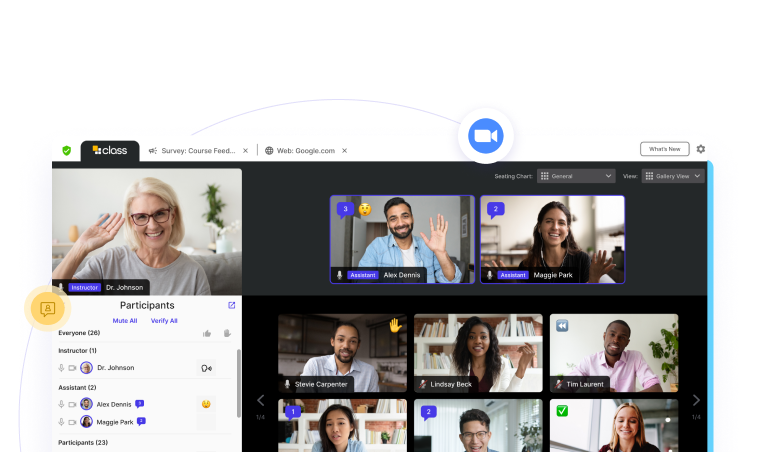
Sign up for a product demo today to learn how Class’s virtual classroom powers digital transformation at your organization.
Features
Products
Integrations